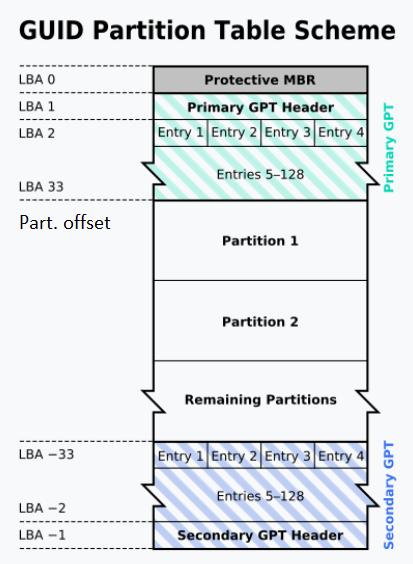
In a previous article (here), we had seen how to convert a GPT disk to a MBR disk, without any data loss.
As indeed, your disk record (MBR or GPT) is actually only a header (i.e before your actual filesystem) pointing to your partition (aka volume aka filesystem…).
Of course, I would strongly advise not to do it against a production system (or at least not without a 200% trusted backup…).
This time, lets do it all from the command line:
rem create a fixed vhd, 512MB, to play with
vmount createfixedvhd f:\disk.vhd 512
rem attach the fixed vhd - note the disk number
vmount attachvhd f:\disk.vhd
rem create a MBR disk against the newly created physicaldrive
Rem make sure to adapt the disk number here!!!
vmount createdisk \\.\PhysicalDrive2 MBR
rem create a MBR part - a format window should popup, go for it
rem also note the offset and size like offset:1048576 & size:534773760
vmount createpart \\.\PhysicalDrive2 MBR
rem put some file on your MBR drive as a test for later
Rem lets pause
rem note : you only really need this second par
rem : the part above was meant to create a test disk
Pause
rem delete the disk to layout (not the data)
vmount deletedisklayout \\.\PhysicalDrive2
rem create a GPT disk
vmount createdisk \\.\PhysicalDrive2 GPT
rem create a GPT part with same offset and size as above
vmount createpart \\.\PhysicalDrive2 GPT 1 1048576 534773760
rem tada...you should now have a GPT drive, with your test file from previous step